How to Check Software Security Before You Buy
Security history is not in the demo.
You found a tool that does everything you want. The demo looked good. The price works.
Six months in, customers get strange emails. Some of your team’s messages disappear. What happened? A security breach. The vendor steps in, you scramble, and move on.
A few weeks later, you lose access to your data. The vendor investigates. Another exploit. They promise a quick fix and say you’ll be back up soon.
Now you’re worried. Someone finally checks what should have been checked before you signed the contract:
The software’s security history.
Ask Before You Buy
- Are the vendor’s compliance certifications relevant to your business?
- What’s their vulnerability disclosure policy?
- Where does your data go, and who can access it?
- What happens to your data if the vendor shuts down or you cancel?
- Have they had a breach? If so, how did they handle it?
The History Nobody Checks
I first wrote about checking software security histories back in 2008, when Secunia my go-to database. The tools are better now, but the value remains the same.
In 2025, a company selling car parts online came to me after their forum software was compromised. The exploit was ugly — an unauthenticated remote code execution flaw that let attackers take over servers without logging in. They’d picked the platform the year before because they were familiar with it.
Based on a security review, I would have gone with XenForo over their choice. Transparent vulnerability disclosure. Fast patches. Modern codebase. That’s what fifteen minutes of checking would have shown them.
I recommend you focus on three areas when evaluating software security:
- Vulnerability history. How many issues has the product had? How fast did the vendor fix them? Did they fix them at all?
- Active exploitation. Is anyone attacking this software right now?
- Vendor transparency. Does the company admit and fix security issues, or do they hide them?
HubSpot in Fifteen Minutes
Say you’re looking at HubSpot as your CRM.
Go to cvedetails.com and search for “HubSpot.” You’ll see a few CVEs, mostly medium-severity issues in the HubSpot WordPress plugin — flaws in the meeting widget or the proxy endpoint. Technical issues, but low severity and patched. The core platform has very few entries. For a tool this popular, that’s a small footprint.
Next, check HubSpot’s security page. SOC 2 Type 2 report? Available. Bug bounty program? Yes. Encryption at rest and in transit. 99.95% uptime SLA. A Trust Center with compliance docs. That’s transparency.
That took fifteen minutes. Now you have a baseline. You can compare any other vendor the same way.
Red Flags Haven’t Changed
The HubSpot review looked clean. Not every vendor will. The same patterns I flagged years ago still show up. Here’s what to watch for.
🚩 Red Flags
- Unresolved critical issues — Known vulnerabilities that have been open for months mean the vendor can’t or won’t fix them.
- Recurring issue types — The same class of flaw (SQL injection, XSS) appearing repeatedly points to a deeper code problem.
- No public security info — A long list of fixed issues is less worrying than silence.
To see how this plays out in practice, here’s a side-by-side of two popular SMB CRMs using the same public data sources anyone can check:
| HubSpot | Zoho CRM & Ecosystem | |
|---|---|---|
| Architecture | Unified SaaS — patches applied centrally across all customer portals | Federated ecosystem (50+ apps); some components offer on-premise versions requiring manual updates |
| CVE profile (2024–2026) | Low volume; most issues in third-party WordPress plugins, not the core platform | Higher volume; includes first-party SQL injection (CVE-2025-8324, severity 9.8), XSS, and authentication bypass flaws |
| CISA KEV catalog | Zero entries (2024–2026) | Multiple entries across the broader Zoho/ManageEngine suite, including vulnerabilities exploited by state-sponsored actors |
| Incident response | June 2024: unauthorized access to fewer than 50 portals detected, investigated, and disclosed within 20 days | Critical SQL injection patches released as “upgrade packs” — on-premise users responsible for applying them |
| Compliance | SOC 2 Type II, SOC 3, ISO 27001 | SOC 2 Type II, ISO 27001, ISO 27017, ISO 27018 |
| Transparency | Trust Center with downloadable reports; Bugcrowd bug bounty program | Security advisories published; documented disclosure process |
Neither platform is good or bad. The data tells different stories. One has a small CVE footprint, mostly in third-party integrations. The other has a broader attack surface and higher-severity core vulnerabilities. It’s also in the CISA catalog. Both have industry-standard compliance certifications.
The point isn’t which CRM you choose. It’s those fifteen minutes with public data. That’s information most buyers never see.
Five Free Vulnerability Databases
A few free databases worth bookmarking:
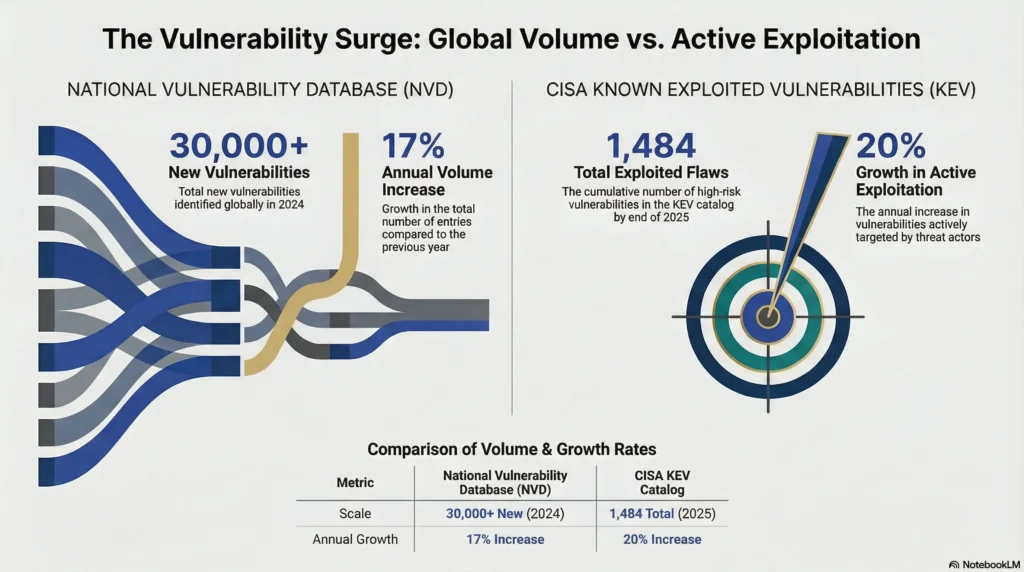
- National Vulnerability Database (NVD) at nvd.nist.gov — the federal government’s CVE database with severity scores and product identifiers. Researchers identified over 30,000 new vulnerabilities in 2024, a 17% jump from the year before.
- CISA’s Known Exploited Vulnerabilities (KEV) catalog at cisa.gov — tracks vulnerabilities actively exploited in real attacks. Nearly 1,500 entries and growing 20% year over year.
- CVE Details at cvedetails.com — easier to browse than NVD, with vendor-level summaries.
- GitHub security advisories — for open-source software, check how fast and how openly the team responds.
- The vendor’s own site — a security page, changelog, or disclosure policy. If you can’t find any mention of security issues, it’s not perfect software. It’s poor communication.
For a solid primer on how CVEs work and how to read them, Sucuri’s beginner’s guide to the CVE database is worth a read.
Your Data, Their Infrastructure
In 2008, most software ran on your servers. You downloaded it, installed it, and controlled it. Now, most business tools are SaaS. You don’t install anything. Your data lives on someone else’s infrastructure. That changes what you need to check. It’s not just about bugs. It’s about whether the vendor protects your data, controls access, handles incidents transparently, and will still be around in two years.
Verizon’s 2025 Data Breach Investigations Report found that 30% of breaches involved a third-party vendor — double the rate from the prior year. That’s not a vendor problem. That’s a due diligence problem.
For AI tools, it’s even less clear. Many are new, built quickly, and haven’t been tested as thoroughly as older software. A short security history doesn’t mean the product is safe. It usually means nobody’s had time to find the problems yet.
Recently, Anthropic used Claude to find over 500 high-severity vulnerabilities in open-source projects. Some had gone undetected for decades. Hackers use the same tools. The window between a vulnerability and someone exploiting it keeps getting shorter.
If you’re evaluating an AI vendor:
- What can you tell me about the training data used for your model? Was sensitive or proprietary information included?
- Are your model’s data handling procedures documented and open to review?
- How do you handle and protect user prompts and outputs? Are they stored, and if so, for how long?
The Business Question
The tools for checking are better than in 2008. The databases are bigger. The information is easier to find. Vendors who ignore security are more likely to get called out.
But the gap is still there. People compare features. They haggle over price. Security checks don’t happen. Not because it’s hard, but because nobody thinks to ask.
Fifteen minutes of research before you sign is worth more than any incident response plan after a breach. Most people skip it. That’s the risk.

Jeff Huckaby · Founder, RackAID
How I use AI in my writing and editing process
25 years on both sides of vendor relationships. Quoted in Inc. and Entrepreneur. I know what good delivery looks like.
